Microsoft has released today its monthly batch of security updates, known as Patch Tuesday. This month, the OS maker has fixed 56 security vulnerabilities, including a Windows bug that was being exploited in the wild before today’s patches.
Category: Banner Slider
SPY PIXELS – Email Tracking
“See who’s tracking your email” What if we tell you that all our emails are being tracked and our information is being collected. Yes, it is high time we take security seriously and understand the gravity of the scenario. SPY PIXELS: To start with, let us first understand what spy pixels are. Spy pixels which are also known as tracking pixels or web beacons. They are invisible and tiny image files( .PNGs and .GIFs) which are inserted in the content body of an email. They may appear as clear, white…
COMMON VULNERABILITIES AND EXPOSURES – Jan 2021
“STAY UPDATED” CVE Updates for the month of January 2021: Microsoft fixes 83 security bugs in the January 2021 Patch Tuesday releases. For the month of January, Microsoft has patched a total of 83 vulnerabilities across a wide range of products, including Apple, CISCO, Adobe, Chrome, Mozilla, Microsoft checkpoint, Redhat and also Windows operating system, cloud-based products, developer tools, and enterprise servers. But of all the bugs patched, the most important one is a zero-day vulnerability in the Microsoft Defender antivirus, which Microsoft said was exploited before the patches were…
Manchester United Cyber Attack
“A Cyber Gun to the Head” The Red Devils were attacked and it is believed that the cyber criminals are holding them to ransom for millions of pounds after hacking into their system. Manchester United released a statement late on Friday, 20 Nov of an attack on their IT systems that took place that very evening. The attack was identified and shut down by the cyber defences set up by the club’s IT team. It’s rumoured to be a ransomware attack for which the club has neither agreed or denied…
Identity and Access Management
Data is the most important thing when it comes to cybersecurity. To protect one’s data, we should be aware of who has access to the data, only the authorized person with defined permissions should be able to access the data. IAM verifies and manages different permissions for different employees according to their role in the organization.
COMMON VULNERABILITIES AND EXPOSURES (CVE) – October 2020
In the fast moving world of cybersecurity, it is necessary for us to stay updated of the latest vulnerabilities and patch them immediately to prevent any incident from occurring.
Networking Protocols
The importance of network protocol, for every work we do there is an established protocol. These protocols are set to determine how the process has to be created and executed. Without these protocols a machine does not understand the signals sent by another machine.
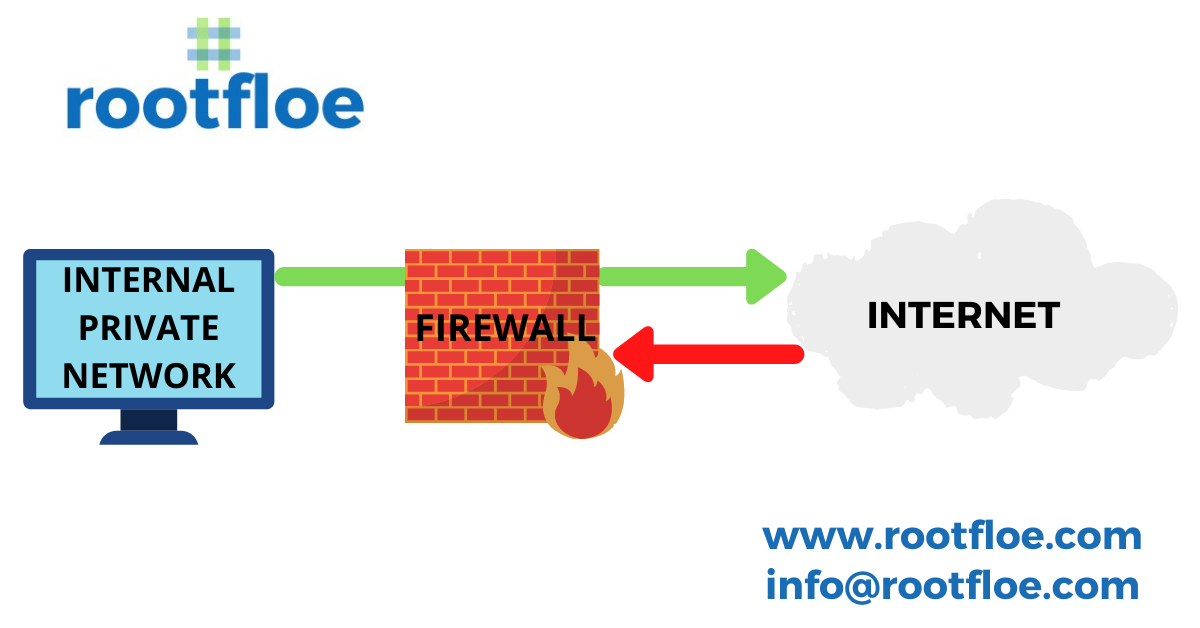
WHAT IS A FIREWALL? – IMPORTANCE & TYPES OF A FIREWALL
There are hackers spreading malicious data to your networks and a firewall acts as a barrier to prevent the entry of malicious data into the network by blocking unknown traffic from entering your network and thereby securing the network from cyber attacks.
Phases of a penetration test
In this article, we will look at the various steps involved in a pen test. Although different frameworks or methodologies might state fewer steps than those listed below, the steps below would be included in one form or another:
Cybersecurity Checklist
A detailed look into cybersecurity checklist that an organisation can follow to avoid any security incidents and financial loss in the future due to poor security posture.