Data is the most important thing when it comes to cybersecurity. To protect one’s data, we should be aware of who has access to the data, only the authorized person with defined permissions should be able to access the data. IAM verifies and manages different permissions for different employees according to their role in the organization.
Author: Nikil
Networking Protocols
The importance of network protocol, for every work we do there is an established protocol. These protocols are set to determine how the process has to be created and executed. Without these protocols a machine does not understand the signals sent by another machine.
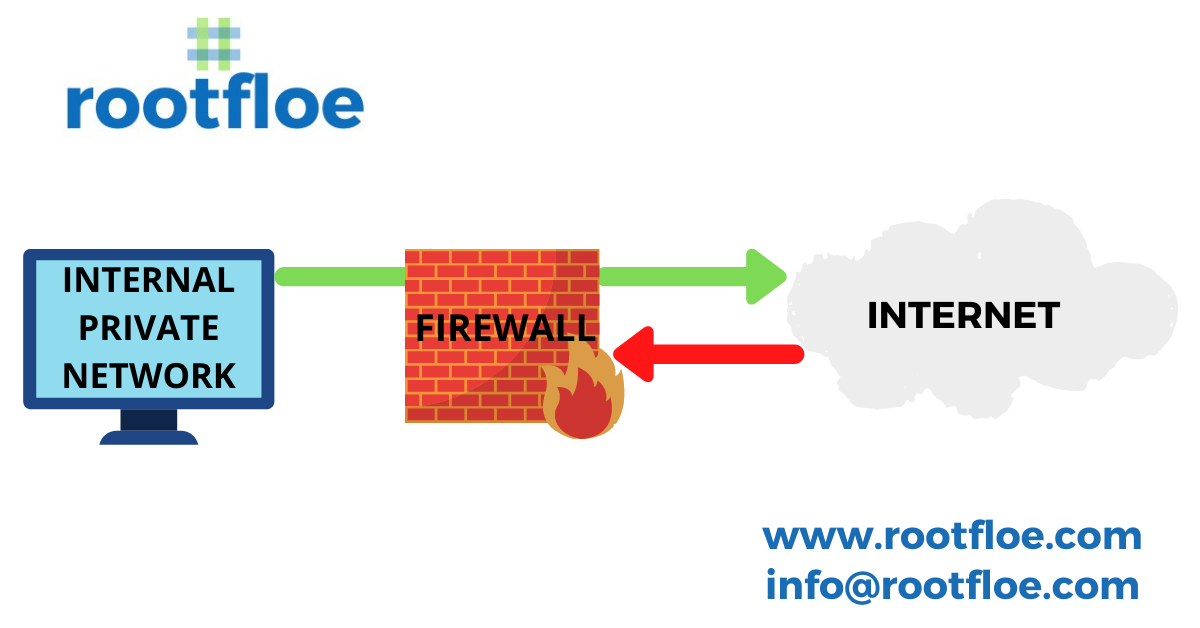
WHAT IS A FIREWALL? – IMPORTANCE & TYPES OF A FIREWALL
There are hackers spreading malicious data to your networks and a firewall acts as a barrier to prevent the entry of malicious data into the network by blocking unknown traffic from entering your network and thereby securing the network from cyber attacks.
NMAP
it is mandatory to scan for errors and bugs in your network and also check for vulnerabilities to prevent an intruder from accessing your network
Encryption Frameworks – Public Key Management
“Encrypt your data or lose it” In today’s modern world, there are millions of websites that provide different services, but how are they doing this? How are they shielding themselves from attackers? Using public Key Management to build a safe environment The Internet is a place where the attackers look out for vulnerable websites and networks and are always looking for a loophole to take advantage of. A cyber criminal can change his identity in no time and make himself anonymous. So attackers are on the lookout for bugs and…