The importance of network protocol, for every work we do there is an established protocol. These protocols are set to determine how the process has to be created and executed. Without these protocols a machine does not understand the signals sent by another machine.
Category: Network Pentesting
WHAT IS A FIREWALL? – IMPORTANCE & TYPES OF A FIREWALL
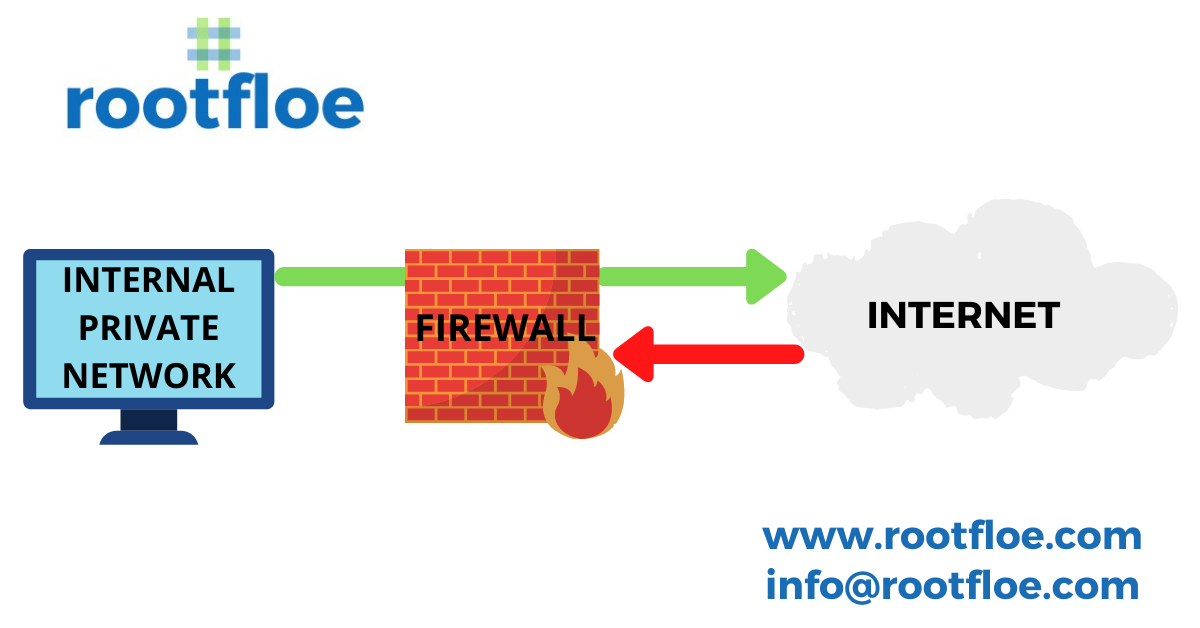
There are hackers spreading malicious data to your networks and a firewall acts as a barrier to prevent the entry of malicious data into the network by blocking unknown traffic from entering your network and thereby securing the network from cyber attacks.
Phases of a penetration test
In this article, we will look at the various steps involved in a pen test. Although different frameworks or methodologies might state fewer steps than those listed below, the steps below would be included in one form or another:
NMAP
it is mandatory to scan for errors and bugs in your network and also check for vulnerabilities to prevent an intruder from accessing your network
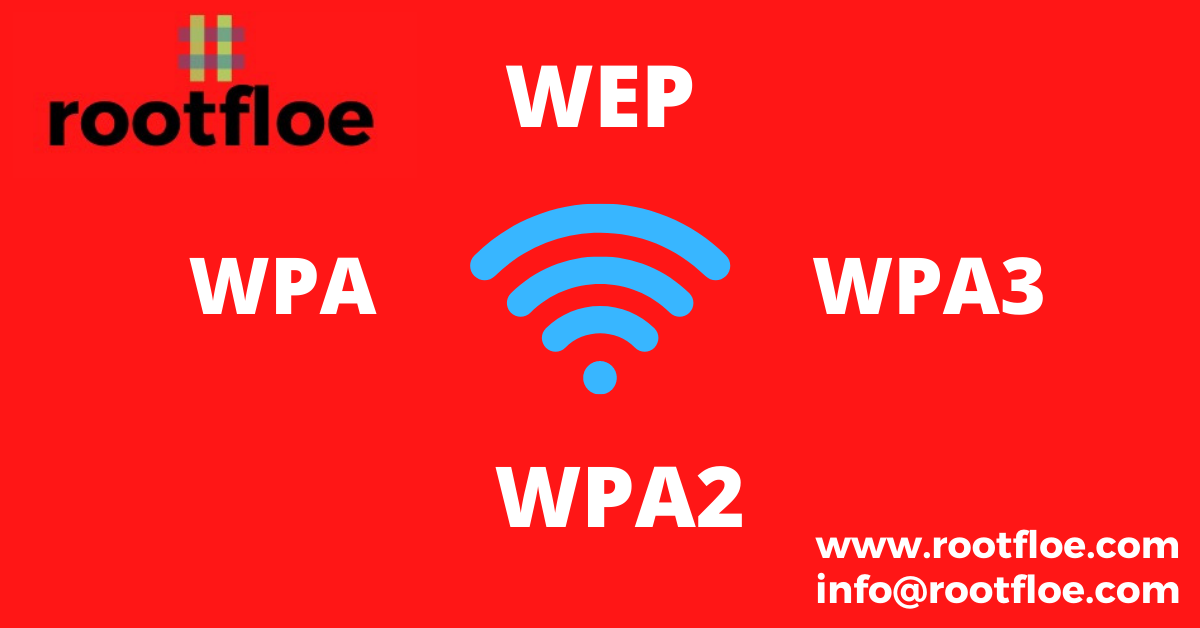
Wireless Security
‘’The era of wireless connectivity is ON! ’’ The world is growing at an enormous pace, technology is at the forefront and ushering the world into the new age of wireless devices surrounding us. The Internet is the medium that connects the whole world together. The 4.57 billion people on the planet Earth use the internet for a variety of different tasks i.e that’s almost 60% of the world total population. Most of this population use a wireless device to access the internet like a smartphone, tablet or a laptop.…
Security Testing
An information security assessment is a process of determining how effectively an entity being assessed (e.g., host, system, network, procedure, person—known as the assessment object) meets specific security objectives