Microsoft has released today its monthly batch of security updates, known as Patch Tuesday. This month, the OS maker has fixed 56 security vulnerabilities, including a Windows bug that was being exploited in the wild before today’s patches.
Category: InfoSec
SPY PIXELS – Email Tracking
“See who’s tracking your email” What if we tell you that all our emails are being tracked and our information is being collected. Yes, it is high time we take security seriously and understand the gravity of the scenario. SPY PIXELS: To start with, let us first understand what spy pixels are. Spy pixels which are also known as tracking pixels or web beacons. They are invisible and tiny image files( .PNGs and .GIFs) which are inserted in the content body of an email. They may appear as clear, white…
FireEye Cyber breach – PART II
No organization is 100% secure – ever! As FireEye continued to investigate and identify the root cause of their security incident, they identified a global campaign that introduced a compromise into the networks of public and private organisations through the software supply chain. FireEye identified that this compromise was delivered through a widely used IT infrastructure management and remote monitoring software – SolarWinds. Although FireEye hasn’t attributed this attack to any particular group, based on several media reports, it is believed that this attack was carried out by a nation-state…
Fireeye Cyber Breach – PART I
No organization is 100% secure – ever! FireEye is one of the world’s renowned cybersecurity firms with customers including major government agencies and enterprise customers around the world. The company is known for its world-class research on state-sponsored threat actors and its incident response capabilities. On 8th December 2020, FireEye CEO Kevin Mandia said in a public statement that they were recently attacked by a highly sophisticated threat actor. “This attack is different from the tens of thousands of incidents we have responded to throughout the years. The attackers tailored…
Manchester United Cyber Attack
“A Cyber Gun to the Head” The Red Devils were attacked and it is believed that the cyber criminals are holding them to ransom for millions of pounds after hacking into their system. Manchester United released a statement late on Friday, 20 Nov of an attack on their IT systems that took place that very evening. The attack was identified and shut down by the cyber defences set up by the club’s IT team. It’s rumoured to be a ransomware attack for which the club has neither agreed or denied…
COMMON VULNERABILITIES AND EXPOSURES – Nov 2020
“STAY UPDATED” CVE Updates for the month of November 2020: Microsoft released today its monthly roll-up of security patches known as Patch Tuesday. This month they fixed 58 security bugs across a wide range of products, from Microsoft Edge to the Windows WalletService. This month’s patches also include a fix for a Windows zero-day vulnerability that was exploited in the wild. Continuous vulnerability management and cyber hygiene can fend off the majority of cyber-attacks. Stay secure by updating patches and fix your vulnerabilities before they take over your system. Remote…
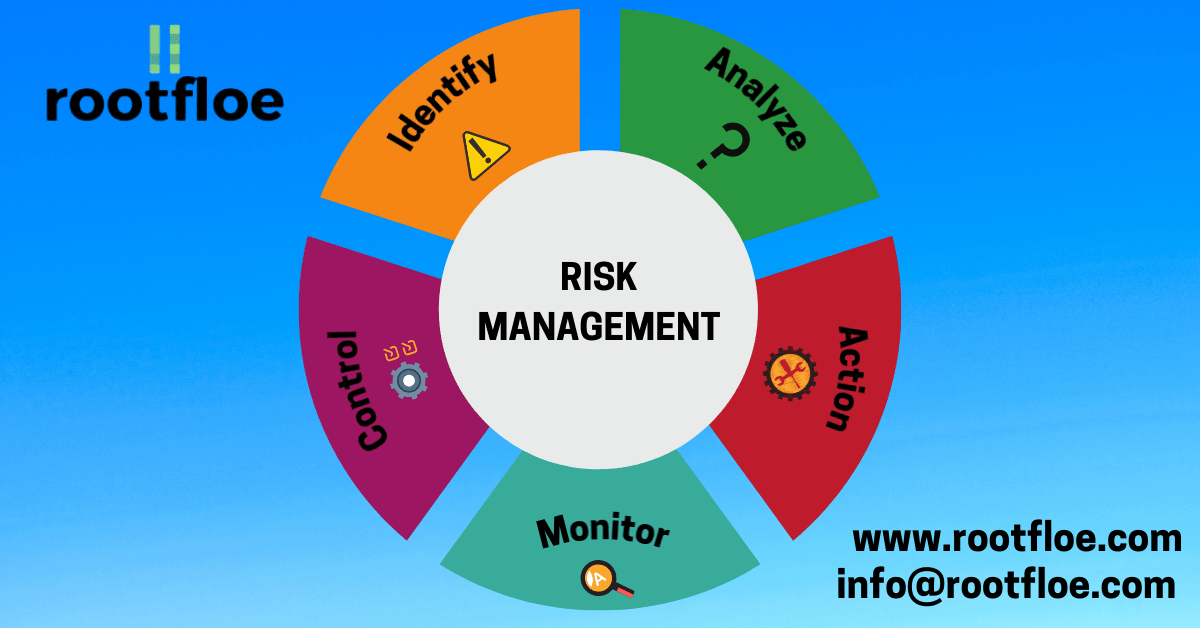
Risk Management
“Be Prepared for Anything!” What is Risk Management? Risk Management can be defined as the process of identifying, evaluation and prioritization of risks and further plan to monitor and reduce the impact of unfortunate incidents. ISO 31000 classifies risk management process into the following steps; communication and consultation; establishing the context; risk assessment, risk identification; risk analysis; risk evaluation; risk treatment; monitoring and review. Risk Management is an iterative process. Why is it important? Risk can come from different sources in and out of an organization. It is important to…
Identity and Access Management
Data is the most important thing when it comes to cybersecurity. To protect one’s data, we should be aware of who has access to the data, only the authorized person with defined permissions should be able to access the data. IAM verifies and manages different permissions for different employees according to their role in the organization.
Networking Protocols
The importance of network protocol, for every work we do there is an established protocol. These protocols are set to determine how the process has to be created and executed. Without these protocols a machine does not understand the signals sent by another machine.
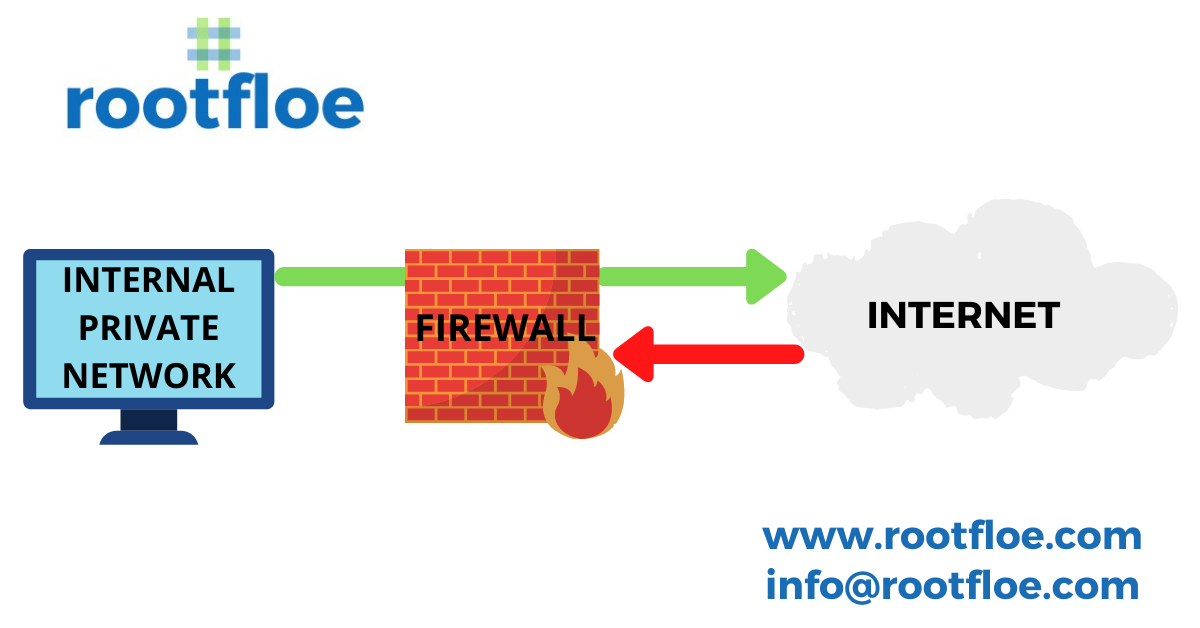
WHAT IS A FIREWALL? – IMPORTANCE & TYPES OF A FIREWALL
There are hackers spreading malicious data to your networks and a firewall acts as a barrier to prevent the entry of malicious data into the network by blocking unknown traffic from entering your network and thereby securing the network from cyber attacks.