“Be Prepared for Anything!”
What is Risk Management?
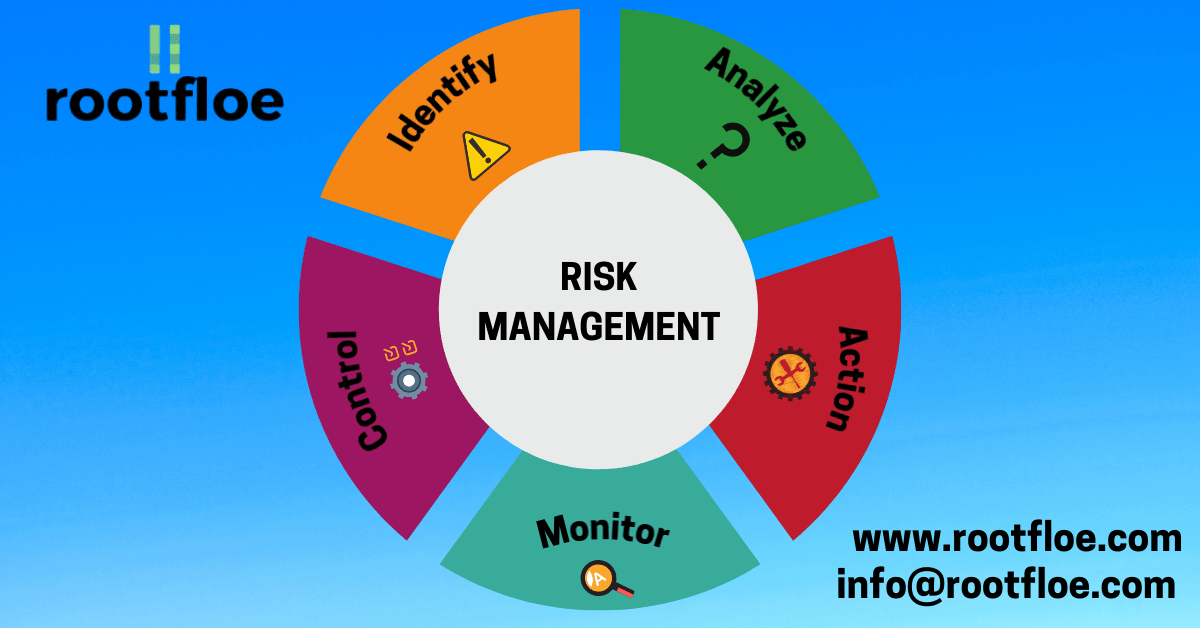
Risk Management can be defined as the process of identifying, evaluation and prioritization of risks and further plan to monitor and reduce the impact of unfortunate incidents.
ISO 31000 classifies risk management process into the following steps;
- communication and consultation;
- establishing the context;
- risk assessment,
- risk identification;
- risk analysis;
- risk evaluation;
- risk treatment;
- monitoring and review.
Risk Management is an iterative process.
Why is it important?
Risk can come from different sources in and out of an organization. It is important to have a risk management plan in place to avoid any security incident from taking place or reduce the impact caused by such incidents.
By implementing a risk management plan, it becomes easier for the organization to assess their security structure and prevent incidents from happening. This helps the organization to save a lot of money and protect their assets.
The Risk Management Process:
A risk is a combination of the consequences that would follow from the occurrence of an unwanted event and the likelihood of the occurrence of the event. Risk assessment quantifies or qualitatively describes the risk and enables managers to prioritise risks according to their perceived seriousness or other established criteria.
- Risk Assessment: The risk assessment process is performed to determine the value of information assets, identifies threats and vulnerabilities, identifies existing controls and their effect on risk,determines the potential consequences and prioritises risks and ranks them against the risk evaluation criteria.
- Risk Identification: After establishing the context, the next step in the process of managing risk is to identify potential risks. Risks are about events that, when triggered, cause problems or benefits. Hence, risk identification can start with the source of our problems and those of our competitors (benefit), or with the problem consequences.
- Risk Analysis: Once the risks are identified, the next step would be to determine the odds of that occurring and the impact of such incidents. Risk analysis may vary in detail, depending on criticality of assets, extent of known vulnerabilities; and prior incidents involving the organisation. There are two types of Risk Analysis,
- Qualitative Risk Analysis
- Quantitative Risk Analysis
- Qualitative Risk Analysis: Qualitative risk analysis uses a scale of qualifying attributes to describe the magnitude of potential consequences (e.g. Low, Medium and High) and the likelihood that those consequences will occur. An advantage of qualitative analysis is its ease of understanding by all relevant personnel while a disadvantage is the dependence on subjective choice of the scale. Qualitative risk analysis may be used:
• as an initial screening activity to identify risks that require more detailed analysis;
• where this kind of analysis is appropriate for decisions;
• where the numerical data or resources are inadequate for a quantitative risk analysis.
- Quantitative Risk Analysis: Quantitative risk analysis uses a scale with numerical values rather than the descriptive scales used in qualitative risk analysis for both consequences and likelihood, using data from a variety of sources. The quality of the analysis depends on the accuracy and completeness of the numerical values and the validity of the models used. Quantitative risk analysis in most cases uses historical incident data, providing the advantage that it can be related directly to the information security objectives and concerns of the organisation. A disadvantage is the lack of such data on new risks or information security weaknesses. A disadvantage of the quantitative approach may occur where factual, auditable data is not available thus creating an illusion of worth and accuracy of the risk assessment.
- Risk Evaluation: The risks are then evaluated based on priority and the likelihood of occurrence. The organisation then takes a decision whether the risk is acceptable or not.
- Risk Treatment: There are four different options for risk treatment;
- Risk Acceptance:Risk acceptance or risk retention means, accepting the risk and not taking any other action in order to reduce the risk because we can accept its impact, the consequences.
- Risk Avoidance: When the identified risks are considered too high, or the costs of implementing other risk treatment options exceed the benefits, a decision may be made to avoid the risk completely.
- Risk Sharing: Risk sharing involves a decision to share certain risks with external parties. Risk sharing can create new risks or modify existing, identified risks. Therefore, additional risk treatment may be necessary.
- Risk Reduction: Risk reduction deals with taking mitigating actions in order to reduce the probability of it occurring.
The risk treatment option has to be decided based on the risk assessment, cost and benefits of the treatment.
Information about risk should be exchanged between decision-makers and other stakeholders. Examples of information include: the existence, nature, form, likelihood, severity, treatment, and acceptability of risks.
Every organisation must have a risk management policy in place to secure the assets, safeguard information and data, prioritise risks based on the severity and prevent security incidents from happening.
Get in touch with us today to help you with implementing your Risk management process. Contact us at info@rootfloe.com for a free consultation.
Shivashankar is a Business Associate at Rootfloe and has a masters degree in Cyber security from Royal Holloway University of London.
https://www.rootfloe.com
Business Associate